PQC
Google's quantum threat to Bitcoin: what the paper actually says
TL;DR: A new Google Quantum AI paper shows that breaking Bitcoin's elliptic curve signatures could require fewer than 500,000 physical qubits; that is roughly a 20x reduction from prior estimates. It is a real scientific result. But no machine with even 1% of that capacity exists today, and the paper is a resource estimate, not a timeline prediction. The actual story is that migration work is already underway, and the window to act is measured in years, not minutes.
Watch
The video version of this analysis is available on YouTube.
"Google slashes quantum cracking estimates by 20X creating $600 billion countdown for Bitcoin and Ethereum," ran the CryptoSlate headline. The Quantum Insider declared that "Q-Day Just Got Closer."
The paper behind these headlines comes from researchers at Google Quantum AI, Stanford, and the Ethereum Foundation. The panic does not. The team published a rigorous resource estimate for solving the elliptic curve discrete logarithm problem (ECDLP) on secp256k1, the curve that secures Bitcoin, Ethereum, and most cryptocurrency wallets. The result is a tighter bound on the number of qubits an attacker would need, and it is lower than previous estimates. But "lower" and "feasible today" are not the same thing.
What the paper actually found
The paper, "Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities" (arXiv:2603.28846), was announced on March 30, 2026. Nine authors contributed, spanning Google Quantum AI, UC Berkeley, Stanford, and the Ethereum Foundation: Babbush, Zalcman, Gidney, Broughton, Khattar, Neven, Bergamaschi, Drake, and Boneh.
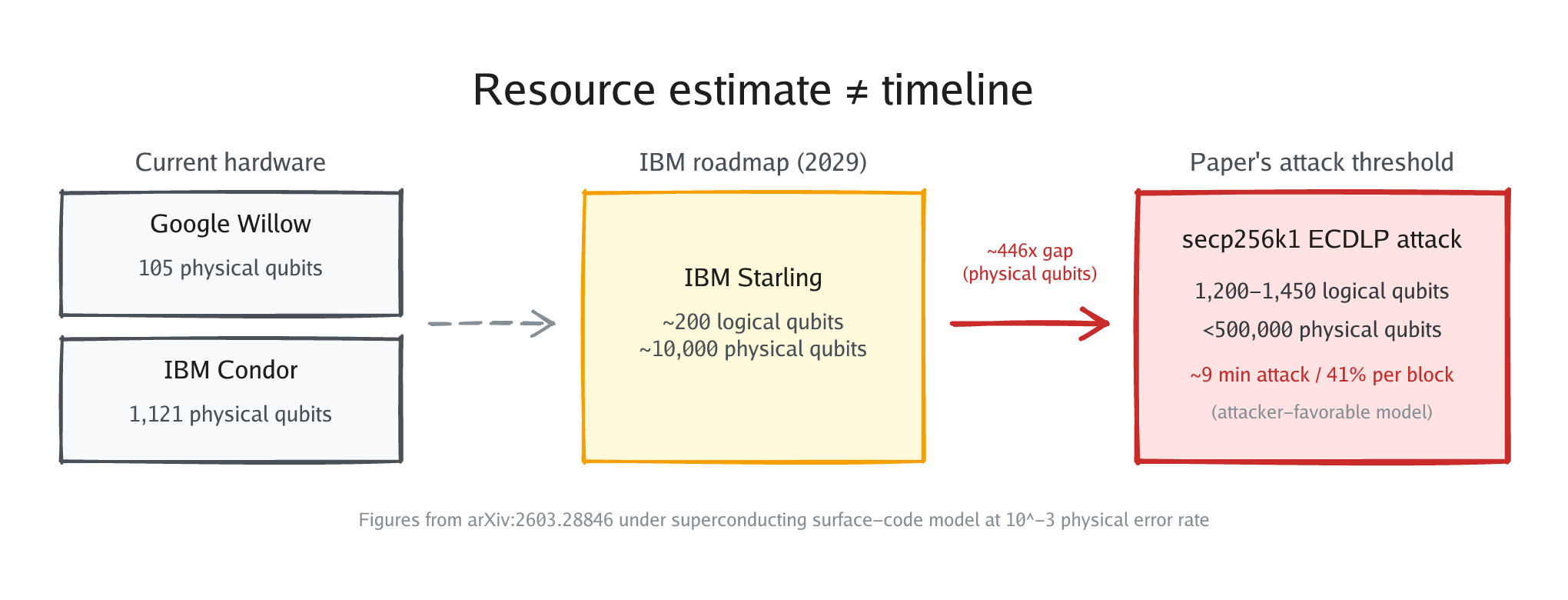
Their central result: solving the ECDLP on secp256k1 requires fewer than 1,200 logical qubits with 90 million Toffoli gates, or fewer than 1,450 logical qubits with 70 million Toffoli gates. Mapped onto a superconducting surface-code architecture at a physical error rate of 10^-3, that translates to fewer than 500,000 physical qubits.
The low-gate variant could execute in roughly 9 minutes from a primed state. Since Bitcoin's block interval is 10 minutes, Figure 6 of the paper shows approximately 41% success probability per block interval. These figures assume an attacker-favorable model: a single-signature target, fast public-key propagation, and no network-level defenses. They describe theoretical capability under idealized conditions, not operational certainty.
These numbers are a roughly 20x improvement over prior estimates. For comparison, Litinski (2023) estimated roughly 7 million physical qubits using a silicon-photonics-inspired architecture, and Webber et al. (2022) estimated 13 million qubits for a 24-hour attack or 317 million for a 1-hour attack.
The improvement comes from algorithmic optimization, not from building a bigger machine. The authors refined the quantum circuit layout for elliptic-curve arithmetic, reduced the number of ancilla qubits required for modular inversion, and optimized the Toffoli gate decomposition. The result is a much tighter resource budget for the same mathematical attack.
One important qualifier: the paper describes a fault-tolerant quantum computer with full error correction running on a surface-code architecture. This is not a near-term NISQ (Noisy Intermediate-Scale Quantum) device. No such fault-tolerant system exists today, and the paper does not claim otherwise.
What it does not say
The paper does not claim anyone can break Bitcoin today. It does not provide a timeline for when such a machine will exist.
Consider the hardware gap. The largest superconducting quantum processor built to date is IBM's Condor at 1,121 physical qubits (December 2023). IBM has since moved past raw qubit count as a metric, focusing instead on modular error-corrected architectures built on its 156-qubit Heron R2 processor. Google's Willow has 105 physical qubits (as of December 2024). The paper's attack requires fewer than 500,000 physical qubits under a specific superconducting surface-code model at a 10^-3 physical error rate; even Condor is 446x short of that threshold, and none of these machines implement the fault-tolerant error correction the attack assumes.
IBM's current fault-tolerant roadmap targets about 200 logical qubits by 2029 with its Starling system, still far short of the 1,200 to 1,450 logical qubits the attack needs. Scaling from roughly a thousand qubits to hundreds of thousands involves unsolved engineering problems in wiring density, cryogenic cooling, and error correction overhead.
The paper also does not claim that quantum computing threatens Bitcoin mining. SHA-256 hashing, which secures Bitcoin's proof-of-work, is resistant to Shor's algorithm. The threat is specifically to ECDSA and Schnorr signatures on secp256k1. A separate paper by Dallaire-Demers (arXiv:2603.25519) examined quantum mining and found that mining at January 2025 difficulty would require on the order of 10^23 physical qubits and 10^25 watts of power. Quantum miners are not a realistic concern.
The paper's value is in tightening the resource estimate so that defenders can plan more precisely. It tells us: "If you build this machine, here is what it costs." It does not tell us when that machine will exist. Those are different questions, and conflating them is how "resource estimate" becomes "Bitcoin cracked in 9 minutes."
The Taproot detail most coverage missed
Bitcoin's vulnerability depends not only on the signature scheme but on how public keys are stored on-chain.
Pay-to-Public-Key-Hash (P2PKH) and Pay-to-Witness-Public-Key-Hash (P2WPKH) addresses store a hash of the public key. The actual key is only revealed when the owner spends the coins. A quantum attacker would need to extract the key from a broadcast transaction and break it before the transaction confirms. That is a much harder timing constraint.
Pay-to-Taproot (P2TR) addresses, introduced in the November 2021 Taproot upgrade, work differently. They expose tweaked public keys as elliptic-curve points on-chain, while the UTXOs (unspent coins) remain unspent. This gives a quantum attacker an indefinite window to work on the ECDLP offline, with no race against block confirmation. Any P2TR UTXO is a standing target.
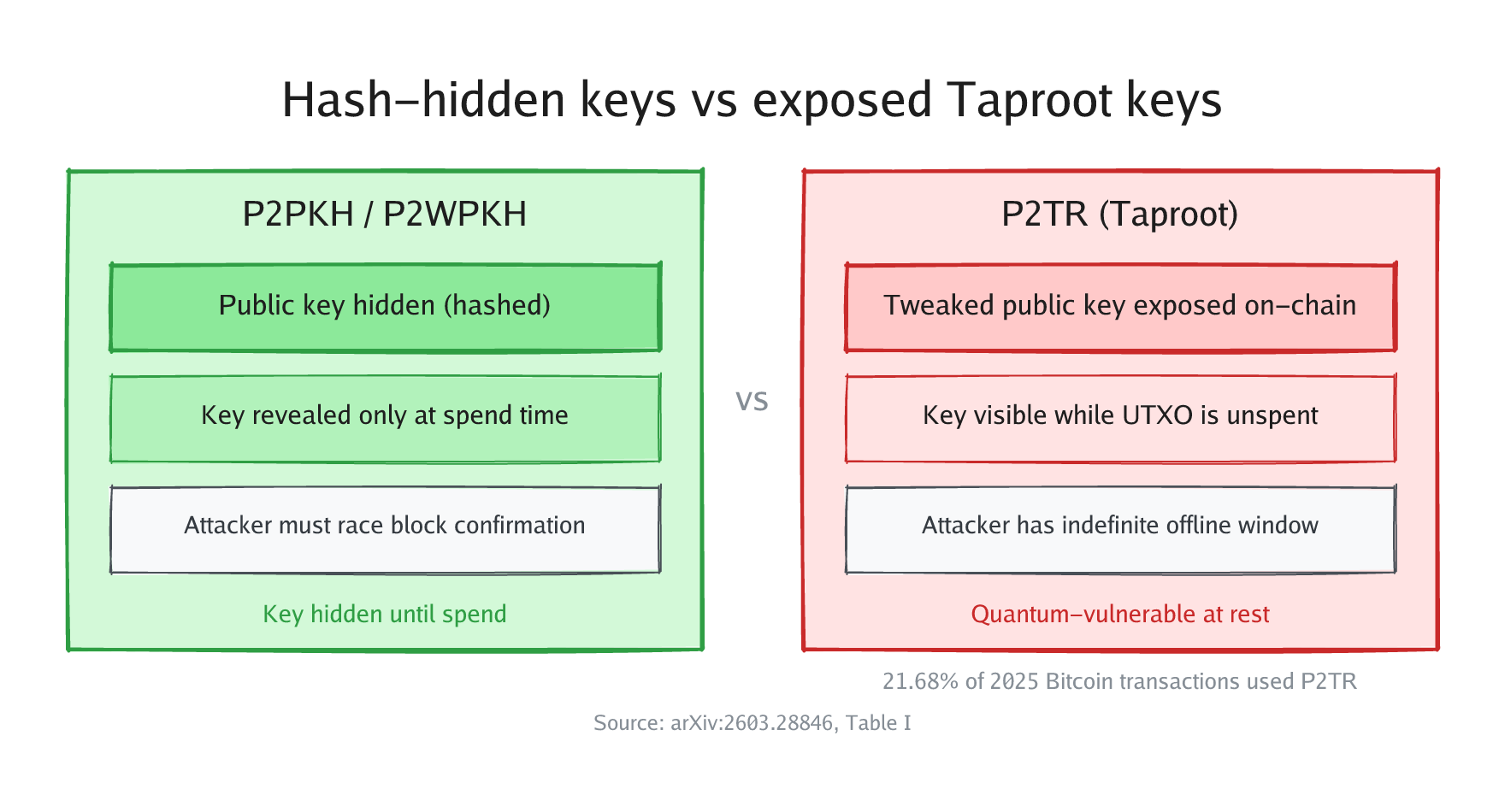
This tradeoff was known at the time. Bitcoin developer Luke Dashjr posted a warning to the bitcoin-dev mailing list on March 15, 2021, titled "PSA: Taproot loss of quantum protections." The community accepted the tradeoff because the quantum threat seemed distant. The Google paper compresses that timeline estimate, making Taproot's offline attack window a more immediate planning concern than it appeared in 2021. The paper's Table I quantifies the exposure: P2TR outputs were associated with approximately 16.8 million BTC moved in 2025, representing 21.68% of all Bitcoin transactions that year. As Taproot adoption grows, so does the amount of Bitcoin held in quantum-exposed outputs.
Migration is already underway
Multiple chains already have post-quantum signature support in production or on testnets.
On the standards side, NIST finalized FIPS 203, 204, and 205 on August 13, 2024, providing standardized post-quantum signature and key encapsulation algorithms (ML-KEM, ML-DSA, and SLH-DSA).
For Bitcoin specifically, BIP-360 (led by Hunter Beast, also known as cryptoquick) defines a new output type called Pay-to-Merkle-Root (P2MR), formerly known as P2QRH and later P2TSH. It was merged into the BIPs repository on February 11, 2026, as a draft proposal (publication in the BIPs repo does not imply community consensus or activation). The BTQ Testnet v0.3.0, deployed on March 19, 2026, is already testing Dilithium-based (ML-DSA) transactions on a Bitcoin fork.
Other chains are further along. The Quantum Resistant Ledger (QRL) has run on XMSS signatures since its mainnet launch on June 26, 2018. Algorand shipped Falcon-1024 post-quantum transactions on its mainnet on November 3, 2025, using logic signature tooling (not a native protocol change, but functional). Solana partnered with Project Eleven to test CRYSTALS-Dilithium (ML-DSA) on a testnet as of December 16, 2025.
Ethereum is funding dedicated post-quantum work. The Ethereum Foundation formed a dedicated post-quantum team in January 2026, led by Thomas Coratger, and launched pq.ethereum.org in March 2026 with $2 million across two research prizes. Justin Drake, one of the nine authors on the Google paper, is an Ethereum Foundation researcher who helped initiate the PQ effort.
The pattern across these projects is consistent: post-quantum signature schemes exist and work, but integrating them into production blockchains is slow due to increased transaction sizes (Dilithium signatures are roughly 2.4 KB versus about 72 bytes for ECDSA), changes to consensus rules, and wallet ecosystem updates. The algorithm is the easy part; the migration engineering is the bottleneck.
What to do with this information
The Google paper does not mean Bitcoin is broken. It means the cost of a future attack is lower than we thought, and the engineering timeline for defense needs to account for that.
For blockchain systems, the primary risk is what this article has focused on: signature forgery against exposed or revealed public keys, especially P2TR outputs and reused addresses. But a related quantum-security concern extends well beyond cryptocurrency. Store-now, decrypt-later means adversaries harvesting encrypted traffic today with the intent to decrypt it once quantum computers are capable. That threat applies to TLS sessions, VPNs, classified communications, and any long-lived encrypted data. This paper's tighter resource estimate makes that timeline harder to dismiss.
Migration to post-quantum algorithms is a multi-year engineering problem for every system that relies on elliptic curve or RSA cryptography. Bitcoin's consensus process makes this especially slow; any change to the signature scheme requires a soft fork, community agreement, wallet updates, and years of testing. The Google paper's contribution is to make the resource estimate more precise, which helps engineers and protocol designers plan with more accurate numbers.
"Years" is not a reason to relax. It is exactly the lead time that protocol upgrades, key rotations, and standard adoptions require. The worst outcome would be treating this paper as either proof of imminent doom or as irrelevant because the hardware does not exist yet. Both readings miss the point.
Read the paper. Read Google's blog post.
Sources:
- Babbush et al., "Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities," arXiv:2603.28846
- Google Research Blog, "Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly"
- Dallaire-Demers, "Kardashev scale Quantum Computing for Bitcoin Mining," arXiv:2603.25519
- Dashjr, "PSA: Taproot loss of quantum protections," bitcoin-dev mailing list, March 15, 2021
- BIP-360 (cryptoquick), bip360.org; official draft: github.com/bitcoin/bips/blob/master/bip-0360.mediawiki
- NIST, "Post-Quantum Cryptography FIPS Approved," August 2024
- QRL mainnet launch, June 2018
- Algorand, "Quantum-Resistant Transactions on Algorand with Falcon Signatures"
- Ethereum Foundation, "Post-Quantum Ethereum," pq.ethereum.org (includes $2M research prize details)
- CoinDesk, "Ethereum Foundation Makes Post-Quantum Security a Top Priority as New Team Forms," January 24, 2026
- Project Eleven + Solana Foundation partnership, December 2025